Forensic examination of computers from an investigative approach
Being able to handle Computer Investigation in-house stands us apart from other private investigators - we don't subcontract the work, enabling the fruits of an investigation to be relevantly applied to other aspects.
Follow the ' See next page - Computer Investigation ' button below for information about what can be achieved, and the immediate action you should take to preserve evidence
Many users think that deleting a computer file, or clearing browsing history will remove the data (and evidence) from their computer - a mistake many have found to their cost. A computer is a mathematical algorithm, and what has been removed can be returned when the machine is investigated; contents of files, with times and dates of when files were created and web sites visited, email and instant message transcripts, images, videos - anything that machine may have been used for since it was built
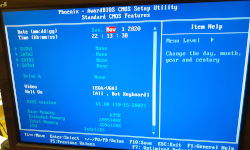
While our methods will adapt from instance to instance, the basics are likely to be:
Computer forensics, put simply, is applying an investigative analysis of a machine's hard drive and external peripherals to obtain legal evidence. Such evidence may be used in a corporate world , when an employee is stealing trade secrets or passing information to a third party, or perhaps in insatnces of internet misuse and fraud.
Retaining the integrity of what may be evidence may be very important - we have suggestions here as to what to initially do
News item in the Daily Telegraph regarding investigation of a computer used in a teacher's class who failed to prevent young pupils accessing pornographic images

We are Corporate Investigators with experience spanning several decades, using such as computer analysis and other forensic tools as an aid to investigation of business affairs

Investigation of your spouse or partner's computer will show the truth of a relationship

First steps to take - what to do with the machine before we collect the unit overnight

The type of evidence that will be gained from examination of a user's computer

Preserving Evidence - how to prepare investigation in best practice

Other evidence on-scene - maintaining the environment and location
Mobile Phone Investigation - on the same principle as computer investigation

